Mac Os Python Crack Password

Generate a Strong Password using Mac OS X Lion’s Built-in Utility Usman June 21, 2012, 7:00am EDT You might’ve heard of the LinkedIn and last.fm security breaches that took place recently.
What is Password Cracking?Password cracking is the process of attempting to gain Unauthorized access to restricted systems using common passwords or algorithms that guess passwords. In other words, it’s an art of obtaining the correct password that gives access to a system protected by an authentication method.Password cracking employs a number of techniques to achieve its goals. The cracking process can involve either comparing stored passwords against word list or use algorithms to generate passwords that matchIn this Tutorial, we will introduce you to the common password cracking techniques and the countermeasures you can implement to protect systems against such attacks.
Topics covered in this tutorial.What is password strength?Password strength is the measure of a password’s efficiency to resist password cracking attacks. The strength of a password is determined by;. Length: the number of characters the password contains.
Complexity: does it use a combination of letters, numbers, and symbol?. Unpredictability: is it something that can be guessed easily by an attacker?Let’s now look at a practical example. We will use three passwords namely1. #password1$For this example, we will use the password strength indicator of Cpanel when creating passwords. The images below show the password strengths of each of the above-listed passwords.Note: the password used is password the strength is 1, and it’s very weak.Note: the password used is password1 the strength is 28, and it’s still weak.Note: The password used is #password1$ the strength is 60 and it’s strong.The higher the strength number, better the password.Let’s suppose that we have to store our above passwords using md5 encryption. We will use an online to convert our passwords into md5 hashes.The table below shows the password hashes PasswordMD5 HashCpanel Strength Indicatorpassword5f4dcc3b5aa7deb882cf991password17c6a180b36896a0a8c02787eeafb0e4c28#password1$29e08fb7103c327d68327f23d8d9256c60. We will now use to crack the above hashes.
The images below show the password cracking results for the above passwords.As you can see from the above results, we managed to crack the first and second passwords that had lower strength numbers. We didn’t manage to crack the third password which was longer, complex and unpredictable. It had a higher strength number. Password cracking techniquesThere are a number of techniques that can be used to crack passwords. We will describe the most commonly used ones below;.
Dictionary attack– This method involves the use of a wordlist to compare against user passwords. Brute force attack– This method is similar to the dictionary attack. Brute force attacks use algorithms that combine alpha-numeric characters and symbols to come up with passwords for the attack. For example, a password of the value “password” can also be tried as p@$$word using the brute force attack. Rainbow table attack– This method uses pre-computed hashes.
Let’s assume that we have a database which stores passwords as md5 hashes. We can create another database that has md5 hashes of commonly used passwords. We can then compare the password hash we have against the stored hashes in the database. If a match is found, then we have the password. Guess– As the name suggests, this method involves guessing. Passwords such as qwerty, password, admin, etc. Are commonly used or set as default passwords.
If they have not been changed or if the user is careless when selecting passwords, then they can be easily compromised. Spidering– Most organizations use passwords that contain company information.
This information can be found on company websites, social media such as facebook, twitter, etc. Spidering gathers information from these sources to come up with word lists.
The word list is then used to perform dictionary and brute force attacks.Spidering sample dictionary attack wordlist 1976 smith jones acme built to last golfing chess soccer.
The buildings themselves, however, are constantly maintained and renewed, thus this age refers to the length of time years for which that particular site has been used as a meeting place.Social significance. The homes are the focus of family identity and tradition, representing the descendants of a founding ancestor. South sulawesi. Dancers perform in front of tongkonan at a Torajan funeralCommon to Toraja of all religions is the cultural centrality of the tongkonan as ancestral homes.
Download now Ethical Hacking using Python Password Cracker Using Python has been published after epic three weeks beta testing, which ended with great success. This tool will NOT let you down and work as described in notes.txt file.For copyright reasons program features won’t be described in this page publicly, to see all instructions and feature list, please download and open.exe file and extract notes.txt file, there is everything that you need for Ethical Hacking using Python Password Cracker Using Python use.All our tools has built in Proxy and VPN support for your anonymity. You can add your own proxy or use our default built in VPN.Ethical Hacking using Python Password Cracker Using Python supports Windows and MAC Os Platforms. And some of the latest mobile platforms.Ethical Hacking using Python Password Cracker Using Python details:- FREE SUPPORT (contact us in our contact form)- Windows, MacOS, iOS, Android support- Proxy and VPN support.- Instructions and full feature list with extras in Notes.txt fileEnjoy!. Other Notes. Cybersecurity Training:.This Edureka Live session on “Ethical Hacking using Python”, we will be discussing how python programming can be used in an ethical hacking engagement.
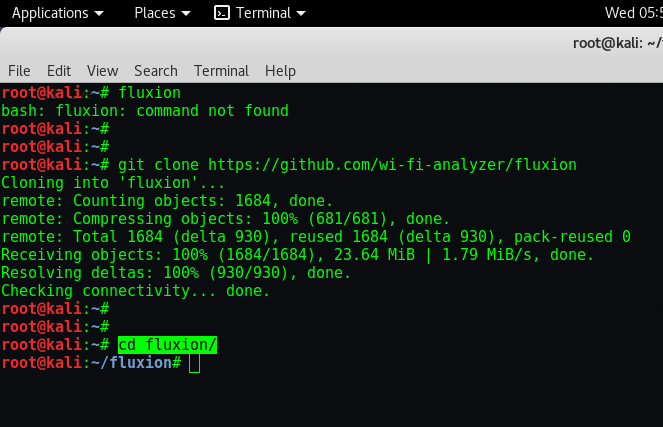
The following topics will be discussed in this live session:What is Ethical HackingWhat is PythonWhy use Python for Ethical HackingDemo: Using Python to build a password cracker.
